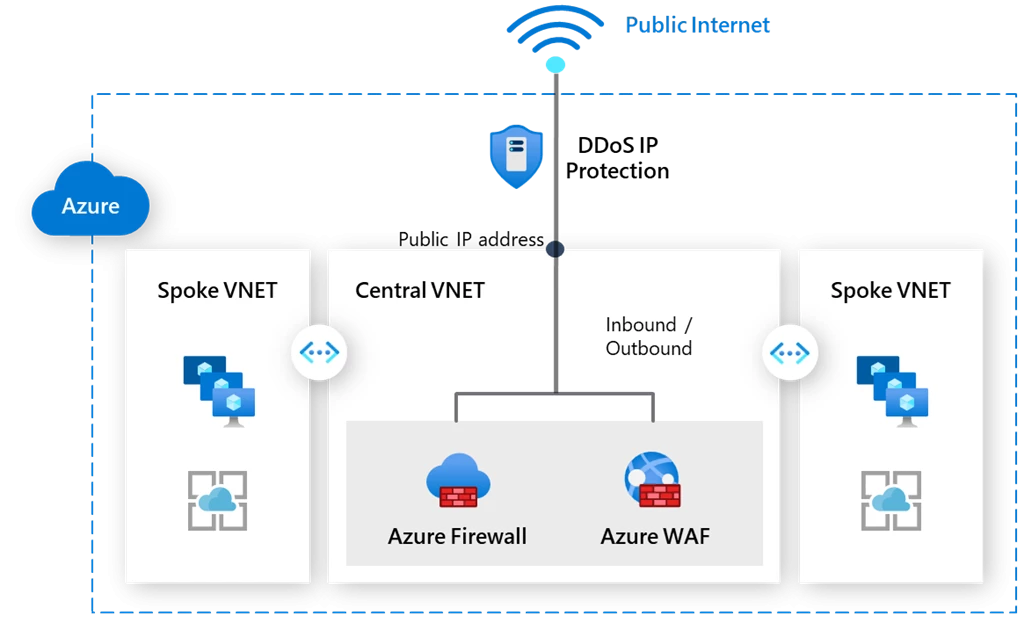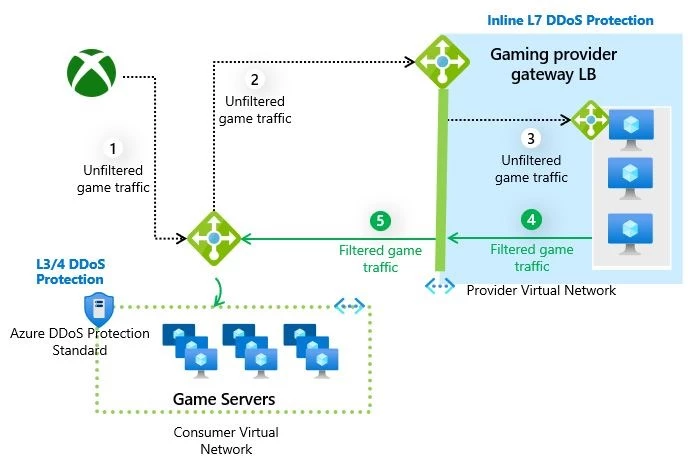
Protect workloads with inline DDoS protection from Gateway Load Balancer partners | Azure Blog | Microsoft Azure
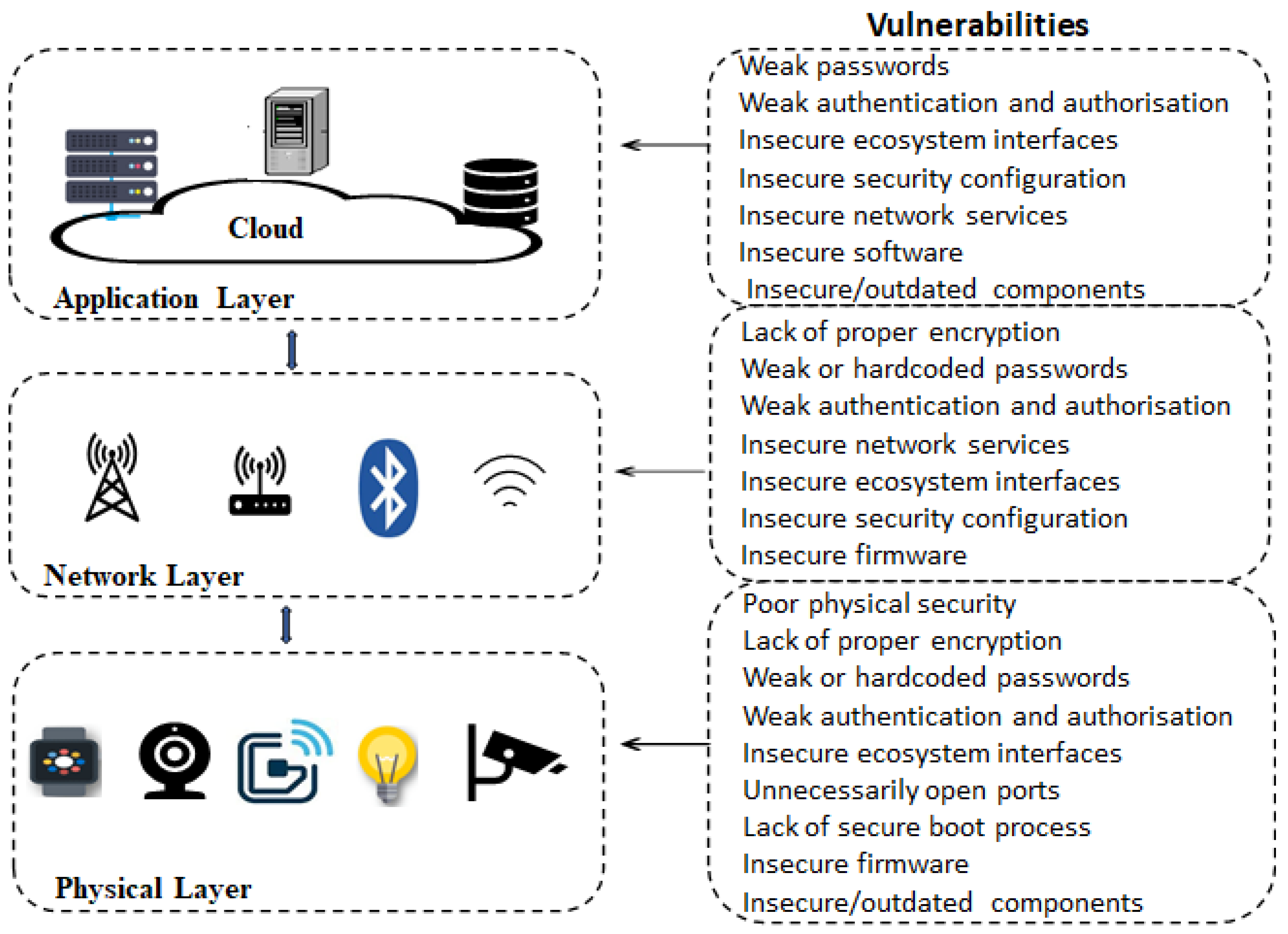
Electronics | Free Full-Text | Analysis of Consumer IoT Device Vulnerability Quantification Frameworks
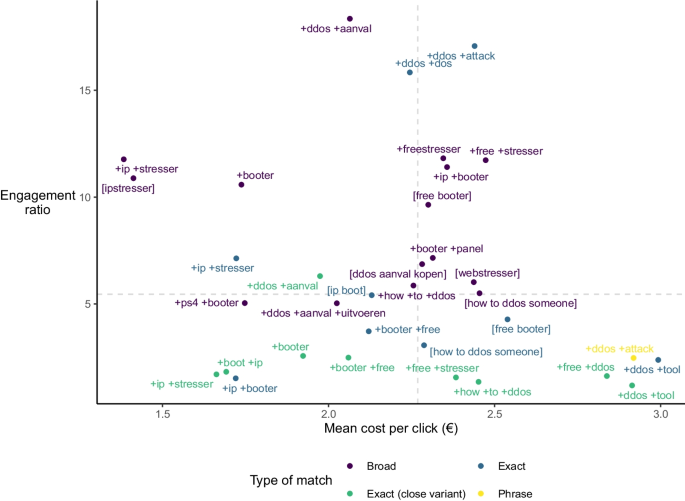
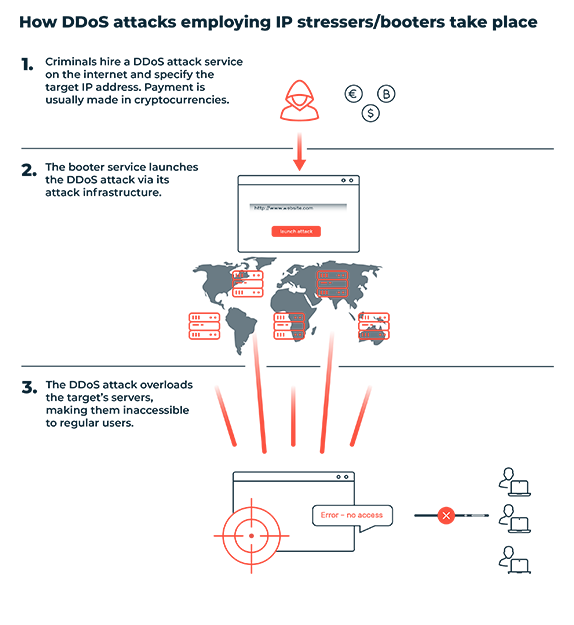
Alerting consciences to reduce cybercrime: a quasi-experimental design using warning banners | SpringerLink